What Really Happens On Your Network? Find Out With Pi-hole
What really happens on your network? Does it come to life when you leave for work? Are there devices connecting to the Internet that you don’t know about? Let’s take a look.
Check out our other iterations of this post:
- Part one: What Really Happens On Your Network?
- Part two: What Really Happens On Your Network?
- Part three: What Really Happens On Your Network?
- Part four: What Really Happens On Your Network?
- Part five: What Really Happens On Your Network?
- Part six: What Really Happens On Your Network?
- Part seven: What Really Happens On Your Network?
- Part eight: What Really Happens On Your Network?

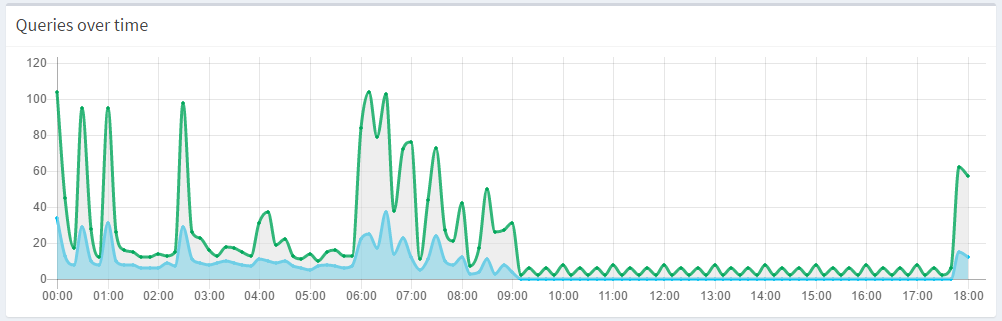
Pi-hole was designed for blocking ads, but it can double as a network monitoring tool because it logs all DNS queries (this can be disabled). Once you setup your router to force your network clients to use Pi-hole as their DNS server, there is nothing else to do except wait and watch what happens.
Unexpected Domain Queries
Whether it’s your smart TV spying on you–or just calling home often–(if you were using Pi-hole, you could have prevented your viewing history from being sent to VIZIO).
Some more examples include strange queries coming from Chrome, a spambot sending out mail, a printer sending out 34 million queries in a day, and lots of torrent activity on your network.
Once installed, you can configure your router so that every device that connects to your network will use Pi-hole as their DNS server. This will allow all the queries happening on your network flow through Pi-hole. This doesn’t slow down your network (in fact it makes things faster), because it only processes DNS traffic, unlike a proxy.
Some More Real Life Examples
IoT Devices Excessively Sending Out Queries
This isn’t terribly surprising because of the nature of smart devices, but some of them do this a bit excessively.
- One example is a user who’s Ring doorbell queried ring.com domains hundreds of times.
- Someone also had an IP camera querying the root DNS servers.
- Another person discovered their Amazon Echo and Harmony Remotes sending all sorts of DNS queries.
- One user’s Hue bulbs were calling home every few seconds.
Certain Brands Of Routers Excessively Phoning Home
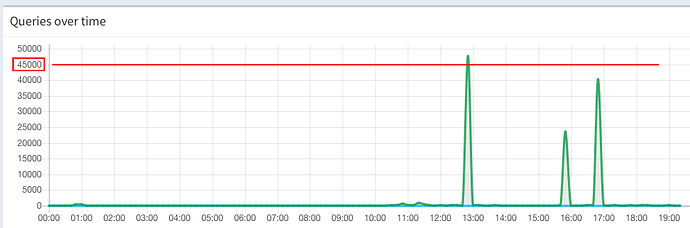
- There is the case of an Eero router sending out excessive queries to node.e2ro.com and eeroup.com (i.e. 50,000 -80,000 queries a day).
- Or a TP-Link range extender with thousands of lookups an hour for tplink.com and some time servers.
- A TPLink Archer7 telemetry domains
- Another example is a Belkin router filling up the query log.
- A DLink router calling home often for the mydlink feature
Porn
- You can decide for yourself what happened with this one.
Microsoft Windows
Users have reported that Windows makes queries to Microsoft domains throughout the day. Most notably, this is previous versions of Windows contacting Microsoft about Windows 10 upgrades (crl.microsoft.com, teredo.ipv6.microsoft.com). Someone also had issues with 300,000 queries relating to the IPv6 protocol in Windows.
Other Examples
- 65,000 queries in one hour from sabnzdb newsreader
- A Pi dialing home to China
- Strange PTR records for a Comcast domain
- A network device accesses the Internet every 20 minutes while someone was away at work
- A brute force SSH attack
- A high amount of queries from SmartThings
- A RAID monitoring agent sending 4300 queries per minute
- 700 queries to Kickstarter in one hour
- Kodi querying google.com
- A Roku sending 1200 queries overnight (when not in use)
- A network querying NTP servers 7,000 times every few hours
- An ASUS router querying dns.microsoft.com every five seconds
- Prutunl VPN phoning home excessively
- Android spyware
- A router querying 91.ip-51-254-101.eu hundreds of times
- A network contacting Netflix when no one uses Netflix
- Odd requests to Comcast domains
- Excessive requests to dns.msftnsci.com via an ASUS router
- Thousands of requests for a . domain in China
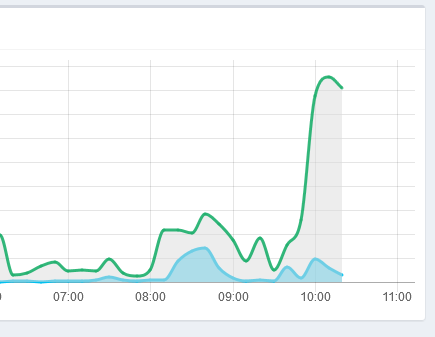
- Huge spike in queries when using Google Earth
- A slew of requests within seconds for several different sites
- Random clients appearing in Top Clients section
- Strange political queries
- An IDS detecting strange queries
